Blockchain
This course is designed to equip students with a comprehensive understanding of blockchain, from the fundamental principles to implementation.
Blockchain
Our blockchain training program offers a comprehensive introduction to this transformative technology, equipping you with the skills to develop robust, secure, and innovative blockchain applications.
Upon completing our blockchain training, you’ll possess the knowledge and expertise to confidently design, build, and debug blockchain applications. This newfound capability will empower you to develop innovative solutions across diverse industries. With our blockchain training, you’ll be well-prepared to tackle the evolving challenges of blockchain. You’ll gain practical experience working with blockchain libraries and tools, enabling you to create and manage your own blockchain projects effectively.
We have Trained professionals from









Equips students with a diverse understanding of encryption methods, spanning from historical ciphers to modern cryptographic algorithms.
Students learn the concept of Reverse Cipher, reversing the order of characters in a message to obscure its original meaning, providing a foundational understanding of a simple encryption technique and its limitations.
Explore the concept of shifting each letter in the plaintext by a fixed number of positions, gaining insights into this fundamental substitution cipher and its application for basic encryption.
The ROT13 Cipher segment, in this specific case of the Caesar Cipher, where the shift is 13 positions, allowing them to grasp a common technique for simple text obfuscation.
Discover the power of data rearrangement in the Transposition Cipher section, unveiling the art of creating a new message order for enhanced encryption through the fascinating technique of permutation.
Unlock the art of data secrecy with the Substitution Cipher module, where each plaintext letter seamlessly transforms into another character, number, or symbol, magnifying the level of security through this elegant process of character substitution.
Learn about using a secret keyword to scramble letters in the message, making the substitution cipher more advanced and customizable in Vigenere Cipher module.

Yes. Tech Cryptors Training Academy is ISO 9001:2015 CERTIFIED COMPANY under IAF. CERTIFICATION will have the significance of the above.
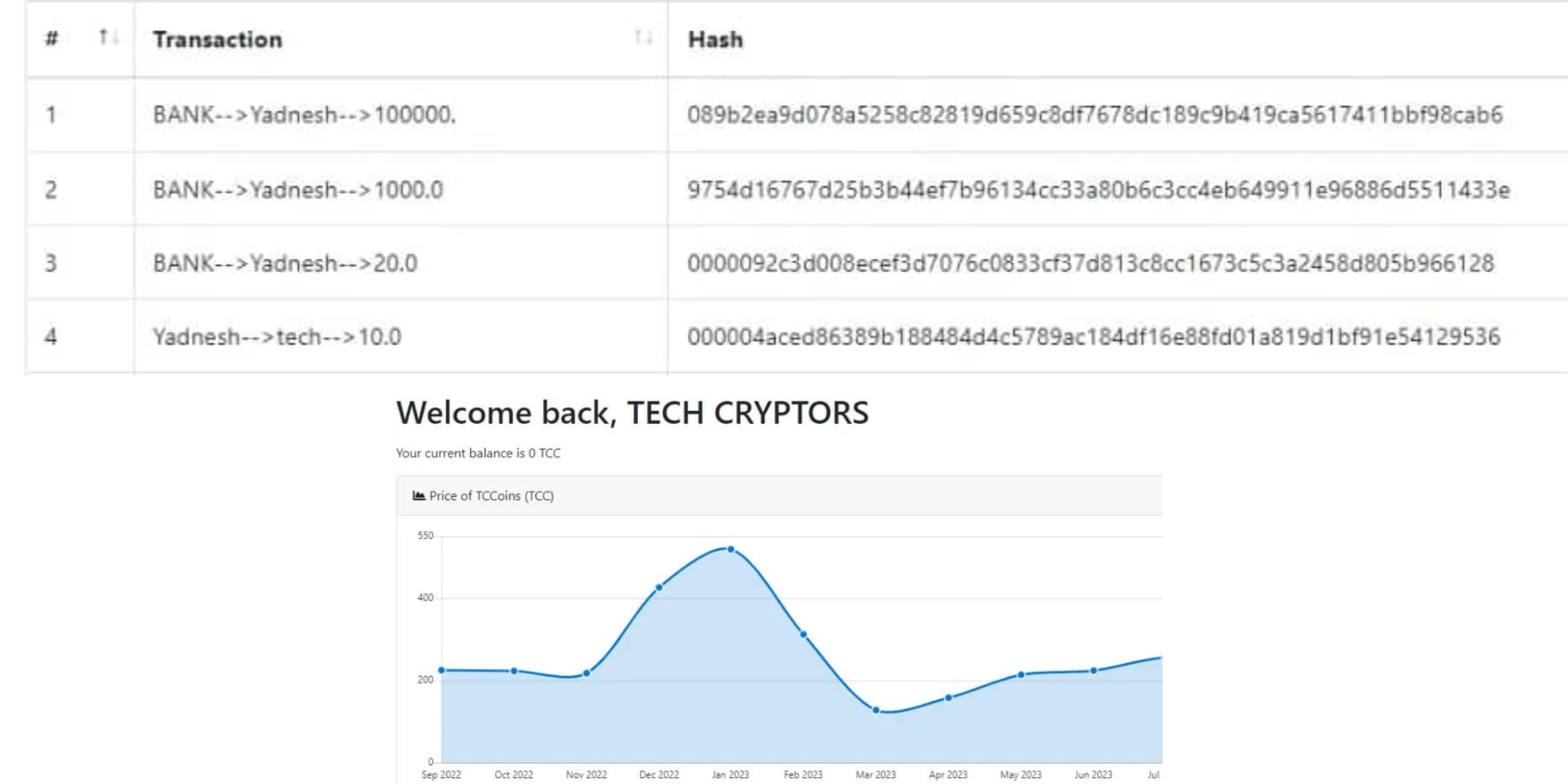
We conduct this course in BOTH online and offline modes. You can choose the mode suitable for you, even you can SWITCH modes for a couple of lectures in case of any personal issues and emergencies.
In one batch we allow MAXIMUM 4 students Because we believe that to have a better understanding and to excel in this course PERSONAL ATTENTION is needed.
We have new batches starting every 15 days, But you should register asap for your desired date because our batches are filling fast. Batch timings are also kept AS PER YOUR TIME CONVENIENCE, we don’t have any rigid preassigned slots.
Well, you can SCROLL DOWN and click on WHATSAPP CHAT text OR CLICK HERE to talk with our customer care executive. We are happy to help you with all of your questions and details.
Students understand the idea of using a super-secret random key that's as long as the message for a super-secure encryption, making the communication extremely confidential when done correctly.
Explore asymmetric cryptography, learning how to secure data transmission and create digital signatures using this essential algorithm in RSA.
Understand the 128-bit hash function MD5, used for data integrity verification, but they also learn about its vulnerabilities, making it unsuitable for modern cryptographic purposes.
SHA1 topic covers the 160-bit hash function SHA1, its historical significance, and its vulnerabilities that limit its use in contemporary cryptography.
Discover the robust SHA3 family of cryptographic hash functions, designed for enhanced security and resistance to specific types of attacks.
The focus here is on the widely used SHA256 hash function, which produces a 256-bit hash value, offering a higher level of security for data integrity and cryptographic applications.
Learn about SHA512, a cryptographic hash function that produces a 512-bit hash value, providing even greater security for applications requiring high levels of data integrity and protection.
Gain a foundational understanding of this distributed ledger technology, exploring its decentralized nature and potential applications across various industries.
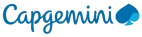
Grasp the structure and importance of transactions in the blockchain, a key element for securely transferring data or assets in transaction class.
Discover how to create a crucial component that interacts with the blockchain network, enabling the sharing and exchange of data in Developing Client phase.
Through the Client Class students delve into the world of object-oriented programming, crafting reusable code to efficiently handle client instances within a blockchain application.
Learn efficiently managing numerous transactions within a block, ensuring the integrity and efficiency of the blockchain's record-keeping process.
Learn Block Class which forms the heart of the blockchain structure, housing transactions and essential metadata, contributing to the cohesive functioning of the blockchain.
Explore the initial block of the blockchain, often with unique information, establishing the foundation for the entire chain In the Creating Genesis Block.
The process of Creating Blockchain covers the practical steps for setting up a blockchain, including configuring parameters, consensus mechanisms, and security considerations.
Through Adding Genesis Block, students learn how to initiate the blockchain by adding the initial block, setting the chain in motion.
Creating Miners introduces students to the role of miners, essential for validating transactions and creating new blocks in proof-of-work blockchain systems.
Learn the Adding Blocks, which involves the continuous expansion of the blockchain, as miners validate transactions and add them to the existing chain, ensuring its continuity.
Learn how to implement Online Crypto Wallet students get hands-on experience in building a web-based wallet, allowing users to interact with the blockchain by sending and receiving cryptocurrencies, providing practical insights into real-world blockchain application development.
Note For Certification
Earn Certificate
Share Your Achivement
Validated by Ethereum

Original Price
₹26,999 /Course
- Max 4 Students per batch
- 1 to 1 Interaction
- Online & Offline mode
- only Video Training
- limited sessions
- Big batches
Current Price
₹19,999 /Course
- Industry level content
- 100% Practical Training
- Experienced Trainers
- Certification for Course
- Corporate Level Examples
- Many other discounts ASK NOW
Reattempt
₹0/Course
- Free Reattempting of Course
- Long Term Support after Completion
- Free Doubt Solving Sessions / Chats
- Discount for Next Courses
- Real-Time Tasks
- Suggestions & Carrer Counselling
